The estimated cost of global cyber attacks will cross $2 trillion by 2019. Despite growing security threats, a recent survey found that 67% of IT teams have a "difficult time understanding which patch needs to be applied to which system."
Why Does Patch Management Matter?
Product patches bring bug fixes and security updates and in some cases, new features and enhancements. The right patches help you fix vulnerabilities for a safe and available infrastructure. Here are some facts that highlight the need for patch management:
- IT professionals are aware of 99% of exploited vulnerabilities for at least a year.
- 44 percent of breaches are due to vulnerabilities that were at least two to four years old.
- The top 10 most common vulnerabilities account for 85% of exploits.
- 75% of attacks use well known issues in commercial software to compromise security.
How do you root out vulnerabilities and ensure 24/7 availability of your IT infrastructure? OpsRamp helps prevent security breaches with timely application of patch updates across your environment. Protect your enterprise with OpsRamp’s automated patching capabilities:
Drive Compliance For Hybrid Environments. How do you keep hybrid infrastructure up-to-date and protected at all times? OpsRamp eases patch management governance across datacenter and cloud in a single interface.
Unparalleled Visibility Across Your Enterprise. How do you cut down the risk of missing out on crucial patches? Track patch compliance levels and mitigate risk exposure with policy based patch management. OpsRamp helps maintain patch baseline levels across different operating system flavors and third party applications in your enterprise.
Patch Management With OpsRamp
OpsRamp provides a consistent and repeatable process for patch compliance and security. Using OpsRamp, you can scan, approve, configure and ratify software patches before deployment. OpsRamp classifies the category, rating and dependency for each patch before installation:
- Category - Category explains what a patch does. For example, Microsoft uses eight patch categories, including critical update, security update, definition update, update rollup, service pack, tool, feature pack and update.
- Rating - Patch ratings help admins prioritize the patch update process. For example, Red Hat uses four severity rating levels, including critical impact, important impact, moderate impact and low impact.
- Dependency - A patch might need to have other patches installed before it can work.
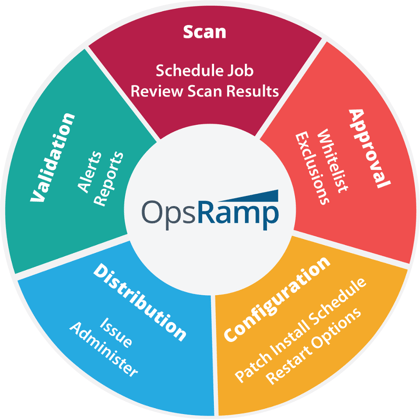
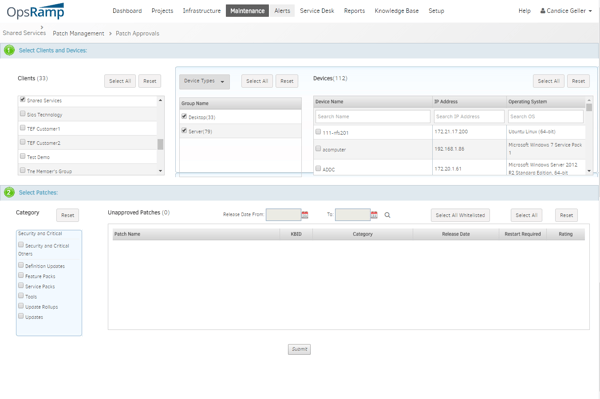
Figure 1 - Patch Management With OpsRamp
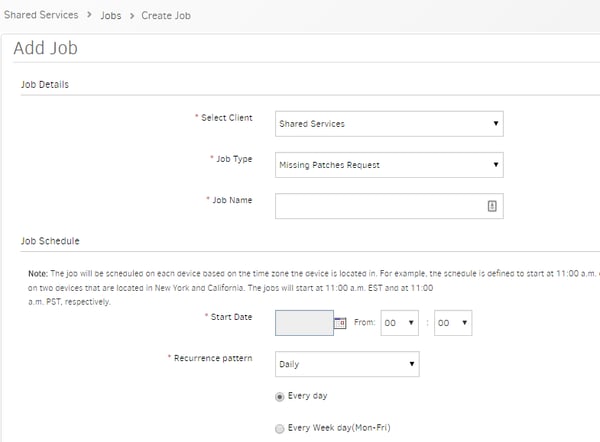
Patch Scan. How do you install the right set of patches for a particular software version? OpsRamp scans and identifies missing patches across different versions of a software package. You can also create jobs in OpsRamp to track missing patches for a version.
Patch Approval. You can manually approve a patch or rate patches using whitelists or exclusions. With a whitelist, you can approve patches globally by selecting several devices at a time. OpsRamp captures all patch approvals for audit trails.
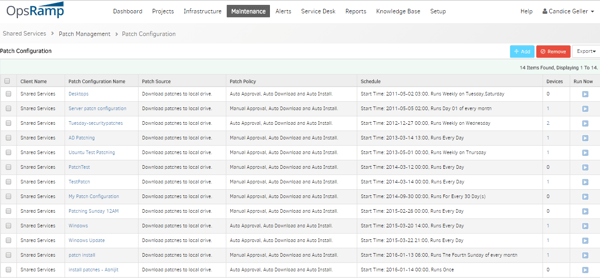
 Patch Configuration. Policy based patching ensure consistent patch levels for threat protection. Patch install schedules help you decide when to apply patch updates. Restart options enforce reboot options after patch installation.
Patch Configuration. Policy based patching ensure consistent patch levels for threat protection. Patch install schedules help you decide when to apply patch updates. Restart options enforce reboot options after patch installation.
Patch Distribution. OpsRamp doesn't distribute patches but acts as a wrapper for distribution. If you use Windows Server Update Services (WSUS) server for Microsoft or a local repo for Linux, the OpsRamp agent facilitates patch deployment. For a Windows device, the Windows Update Agent (WUA) does the actual distribution but OpsRamp invokes the WUA by triggering which patches to install.
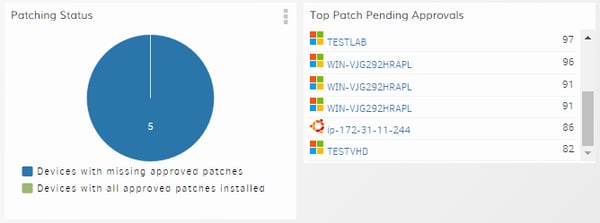
Patch Validation. OpsRamp tracks the status of patch compliance with alerts and reports. Our Consolidated Patches Report displays installed patches, the last patch scan date and install date, and the count of missing patches.
Conclusion
Improve efficiency and mitigate operational risks across your enterprise systems with patch automation. OpsRamp delivers centralized governance and consistent security practices for infrastructure availability, uptime and stability.